Risk Posture Dashboard
A unified view of your organization's identity risk score, showing stale identities, over-permissions, critical junctions, and Tier 0 exposure in a single composite metric.
Requires role: Operator+ Related: Stale Identity Detection, Over-Permission Analytics, Asset Criticality, User Management & RBAC
Overview
The Risk Posture Dashboard provides security administrators and operators with an executive-ready view of identity risk across their entire environment. Instead of reviewing separate analysis reports for stale accounts, over-permissions, junction exposure, and Tier 0 vulnerabilities, the dashboard combines all four signals into a single composite Identity Risk Score (0-100, where 0 is perfect and 100 is critical risk).
This score is calculated using a weighted average of four component metrics:
- Stale Identity Score — Accounts that haven't been used within their type-specific threshold (30 days for computers, 90 days for users, 180 days for service accounts)
- Over-Permission Score — Identities with significantly more access rights than their peers (more than 2 standard deviations above department/title baseline)
- Junction Exposure Score — Identities flagged as critical junctions (high-leverage accounts that connect low-privilege to high-privilege zones)
- Tier 0 Exposure Score — The proportion of Tier 0 assets (domain controllers, domain admins, etc.) that are either stale or over-permissioned
The dashboard is designed to answer three key questions for leadership:
- What is our current risk posture? — The composite score with a letter grade (A/B/C/D/F)
- Is risk trending up or down? — A 30-day trend chart showing score history
- Where should we focus first? — Top 5 highest-risk findings across all categories
Prerequisites
- Role: You must be an Operator or Admin to access the Risk Posture Dashboard
- Data: At least one successful identity sync from an LDAP bridge or Entra ID provider
- Criticality Engine: The criticality evaluation service must be running to compute asset criticality and junction scores (these feed into the composite score)
NOTE
The dashboard can be accessed immediately after your first sync, but trend data will only appear after at least one daily snapshot has been recorded (snapshots are created automatically by the criticality service).
Accessing the Dashboard
The Risk Posture Dashboard is available in two ways:
- Default Landing Page — After logging in, you'll see the dashboard as the first view (when implemented)
- Navigation Menu — Open the navigation menu (☰) and select Dashboard under Main
The dashboard automatically refreshes every 5 minutes and recalculates when you switch back to the browser tab (refetch on window focus).
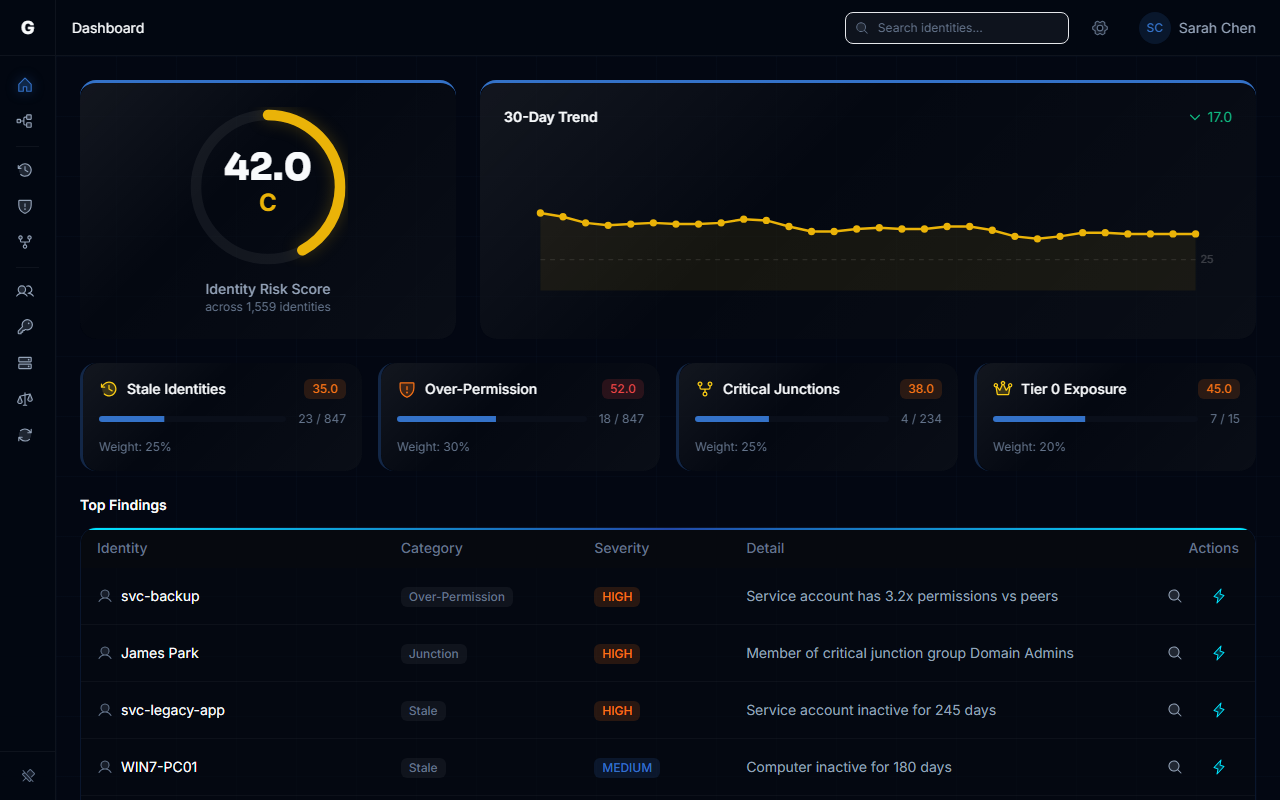
Understanding the Composite Score
The composite score ranges from 0 to 100:
| Score Range | Grade | Interpretation |
|---|---|---|
| 0 - 10 | A | Excellent identity hygiene — minimal findings |
| 11 - 25 | B | Good posture — minor issues that should be monitored |
| 26 - 50 | C | Fair posture — action recommended to reduce risk |
| 51 - 75 | D | Poor posture — significant risk requiring attention |
| 76 - 100 | F | Critical risk — immediate action required |
The score is displayed as a circular gauge with color coding:
- A: Green
- B: Lime
- C: Yellow
- D: Orange
- F: Red
Below the gauge, you'll see:
- The numeric score
- The letter grade
- The total number of identities evaluated
Component Breakdown
The dashboard shows four component cards, one for each risk category. Each card displays:
- Score (0-100) — The normalized finding count as a percentage of total identities
- Finding Count / Total Count — Raw numbers (e.g., "23 / 4200")
- Weight — The contribution of this component to the composite score (default: 25% each)
- Description — A brief summary of what was found
Stale Identity Score
Identities that haven't authenticated within their type-specific threshold:
- Users, Groups, Roles: 90 days
- Computers, Devices: 30 days
- Service Accounts, Service Principals, Applications: 180 days
Example: If 157 out of 4200 identities are stale, the score is approximately 3.7 (very low risk).
Why this matters: Stale accounts are often left enabled after an employee leaves or a system is decommissioned. Attackers target these dormant accounts because they're less likely to be monitored.
Over-Permission Score
Identities with effective permission counts (direct + inherited) that significantly exceed their peer group's average. Peer groups are formed by identity type + department + title (e.g., "User / Engineering / Software Engineer").
Example: If 23 out of 3800 identities are flagged, the score is approximately 0.6.
Why this matters: Over-permissioned accounts violate the principle of least privilege. They represent lateral movement opportunities — an attacker who compromises one of these accounts gains access to far more resources than a typical user.
Junction Exposure Score
Identities flagged as critical junctions — accounts that bridge low-privilege and high-privilege zones in the access graph. These are computed by the criticality service based on betweenness centrality and criticality tiers.
Example: If 8 out of 4200 identities are junctions, the score is approximately 0.2.
Why this matters: Junctions are high-leverage attack targets. Compromising a junction node can provide a path from a low-security entry point (e.g., a compromised user workstation) to Tier 0 assets (domain controllers, privileged groups).
Tier 0 Exposure Score
The percentage of Tier 0 assets (domain admins, domain controllers, enterprise admins, etc.) that are either stale OR over-permissioned.
Example: If 3 out of 12 Tier 0 identities have hygiene issues, the score is 25 — a high-impact finding even though the absolute count is small.
Why this matters: Tier 0 assets have "keys to the kingdom." Even a single stale Tier 0 service account can provide an attacker with persistent domain-wide access.
WARNING
Tier 0 findings are always prioritized in the Top Findings table, regardless of their count, because of their critical impact.
Tracking Trends Over Time
The 30-Day Trend Chart shows how your composite score has changed over the last month. Each data point represents a daily snapshot recorded automatically by the criticality service.
What to look for:
- Downward slope (green arrow): Your risk posture is improving — findings are being remediated faster than new ones are appearing
- Upward slope (red arrow): Risk is increasing — new findings are accumulating or remediation has slowed
- Flat line: Risk is stable — a baseline for comparison
The chart includes a reference line at 25 (the target for a "B" grade or better). This helps you visually track progress toward a desired posture.
NOTE
Snapshots are recorded once per day (UTC). If you remediate findings during the day, the score improvement will appear in tomorrow's snapshot.
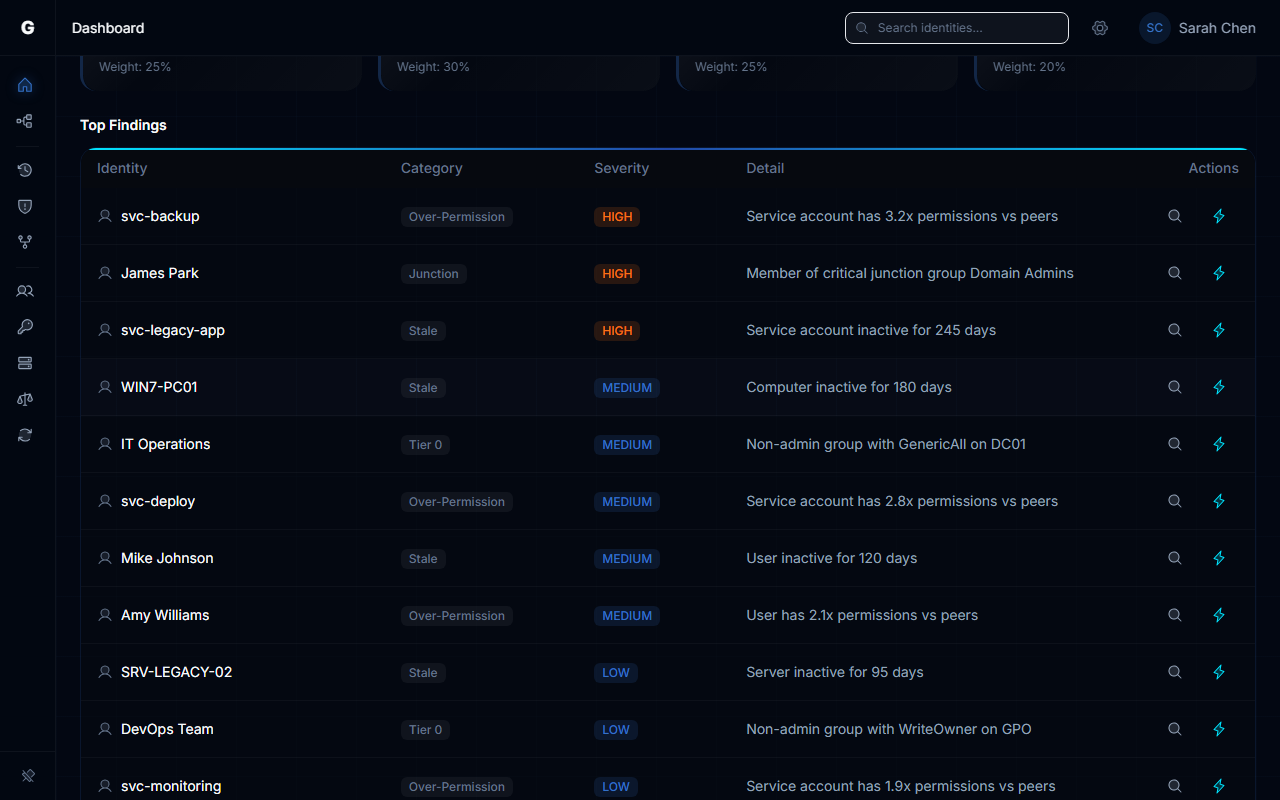
Top Findings Table
The Top Findings section highlights the 5 highest-risk identities across all analysis categories. Findings are sorted by severity:
- CRITICAL: Tier 0 assets with stale or over-permission issues
- HIGH: High-criticality identities or junctions with hygiene problems
- MEDIUM: Other flagged identities
Each row shows:
- Identity: The display name (or ID if no name is available)
- Category: Stale, Over-Permission, Junction, or Tier 0
- Severity: CRITICAL, HIGH, or MEDIUM (color-coded badge)
- Detail: A brief description (e.g., "Stale for 180 days" or "Junction score: 12.4")
Example findings:
| Identity | Category | Severity | Detail |
|---|---|---|---|
| svc-backup-admin | Tier 0 | CRITICAL | Tier 0 asset stale for 180 days |
| DA-HELPDESK | Junction | HIGH | Junction score: 14.2 |
| john.doe | Stale | HIGH | Stale for 120 days |
TIP
Click on an identity name in the findings table to navigate to the Graph Explorer with that node focused (when navigation is implemented).
Customizing Component Weights
By default, each component contributes 25% to the composite score. You can adjust these weights to emphasize the areas most important to your organization.
Example: If Tier 0 hygiene is your top priority, you could set Tier 0 exposure to contribute 40% of the score while reducing the other components to 20% each.
Rules:
- Weights must be non-negative
- Weights are automatically normalized to sum to 1.0 (you don't need to calculate percentages yourself)
- Setting all weights to 0 returns an error
NOTE
In the Beta release, weight customization is available via the settings interface. A more prominent frontend UI for adjusting weights will be added in a future release.
Interpreting Empty or Zero Scores
If the composite score is 0:
- Your environment has no stale identities, over-permissions, junctions, or Tier 0 hygiene issues
- This is the ideal state (Grade A)
- Keep monitoring to ensure risk doesn't drift upward
If a component score is 0:
- No findings were detected in that category
- This is normal for small environments (e.g., if you have no Tier 0 assets defined, the Tier 0 Exposure score will be 0)
If the dashboard shows "No history data available yet":
- The criticality service hasn't recorded a daily snapshot yet
- Snapshots run automatically after each criticality evaluation cycle
- Wait until the next scheduled evaluation cycle (default: every 6 hours) or check the service logs to confirm it's running
Troubleshooting
Dashboard shows "Unable to Load Risk Dashboard"
Possible causes:
No identity data synced — The dashboard requires at least one successful bridge sync or Entra ID sync to have data to analyze
- Solution: Navigate to Bridges in the sidebar and trigger a sync
- Check: Look for identity nodes in the Graph Explorer
Criticality service not running — The criticality engine must be running to compute junction scores and Tier assignments
- Solution: Check that the criticality service container is running in your Docker deployment
- Check: Look for service logs showing "Criticality evaluation cycle completed"
Database connectivity issue — The server couldn't query the database
- Solution: Check server logs for database connection errors
- Check: Verify the
/readyhealth endpoint returns 200 OK
Composite score seems too high/low
Too high (worse than expected):
- Check the component breakdown to see which category is driving the score
- Tier 0 Exposure has an outsized impact because it's calculated as a percentage of Tier 0 assets only (not total identities). A single stale domain admin will produce a high Tier 0 score if you only have a few Tier 0 assets
- Solution: Review the Top Findings table to identify the specific high-impact identities
Too low (better than expected):
- Verify that criticality evaluation has completed (some findings won't appear until tiers and junction scores are computed)
- Check if you have custom thresholds configured that are more permissive than defaults (e.g., a 365-day stale threshold for service accounts instead of 180 days)
Trend chart shows "No history data available yet"
Cause: The criticality service hasn't recorded a daily snapshot yet.
Solution:
- Confirm the criticality service container is running:
docker ps - Check service logs for "Risk posture snapshot recorded" messages
- Snapshots are created automatically after each criticality evaluation cycle (default: every 6 hours)
- If you just deployed the platform, you'll need to wait for the first snapshot to be recorded
Manual trigger (for testing):
The snapshot function is called automatically by the criticality service. There is no manual endpoint to force a snapshot in the Beta release.
Over-Permission score is zero but I know there are over-permissioned accounts
Cause: Over-permission results are pre-computed after each sync and cached per domain. If a sync hasn't completed yet (or analytics failed), the cache may be empty.
Solution:
- Trigger a sync from Bridges in the sidebar — analytics run automatically after sync completes
- Navigate to Analysis > Over-Permissions to see the full findings (the dashboard and analytics page use identical data)
- Check the Sync Metrics panel for the "Analytics" phase timing — if it shows 0ms, analytics may not have run
Top Findings table is empty
Possible causes:
- No findings above threshold — Your environment genuinely has no stale, over-permissioned, junction, or Tier 0 hygiene issues (rare but possible in small environments)
- Criticality not computed — Junction findings require the criticality service to have run at least once
- All findings filtered out — Only CRITICAL and HIGH severity findings appear in the dashboard; MEDIUM findings are not shown
Check:
- Navigate to the individual analysis views (Stale Identities, Over-Permission, Junctions) to see raw finding counts
- Review the component cards to confirm finding counts are non-zero
Related Analysis Features
- Stale Identity Detection — Detailed breakdown of stale accounts by type, criticality, and domain
- Over-Permission Analytics — Peer-group-based detection of identities with excessive effective permissions
- Critical Junctions — High-leverage accounts that bridge privilege tiers
- Asset Criticality Engine — Automated tier assignment and manual overrides
Best Practices
- Set a target score — Aim for a composite score below 25 (Grade B or better). Communicate this target to your security team
- Track weekly trends — Review the 30-day chart every Monday to spot upward risk drift early
- Prioritize Tier 0 findings — Any finding in the Tier 0 category should be addressed immediately, even if the composite score is low
- Automate remediation tracking — Export the composite score to your SIEM or dashboard tool to correlate with other security metrics
- Use the dashboard for executive reporting — The letter grade and trend chart are designed to communicate risk posture to non-technical stakeholders
Performance Notes
- Current posture computation: < 5 seconds (target) for environments up to 100,000 identities
- History query: < 1 second (queries a small document collection, not the full graph)
- Dashboard refresh interval: 5 minutes (client-side polling via React Query)
Over-permission results are pre-computed after each sync and cached per domain. The dashboard reads from this cache, so it loads instantly regardless of graph size. Stale identity, junction, and Tier 0 counts continue to run as lightweight live queries (they are simple index scans that complete in milliseconds).