Tiered Fidelity™: See What's Real, Ignore What's Not
Three evidence tiers that separate validated access from theoretical noise. Fix what matters first.
Every identity security tool finds thousands of "critical" findings. Group memberships that grant powerful access. Role assignments that reach sensitive resources. The problem: most of these paths have never been used. Some are blocked by conditional access or network segmentation. Others exist only because an account was never cleaned up after a role change. When everything is critical, nothing is. Your team wastes weeks chasing theoretical paths instead of real threats.
How It Works
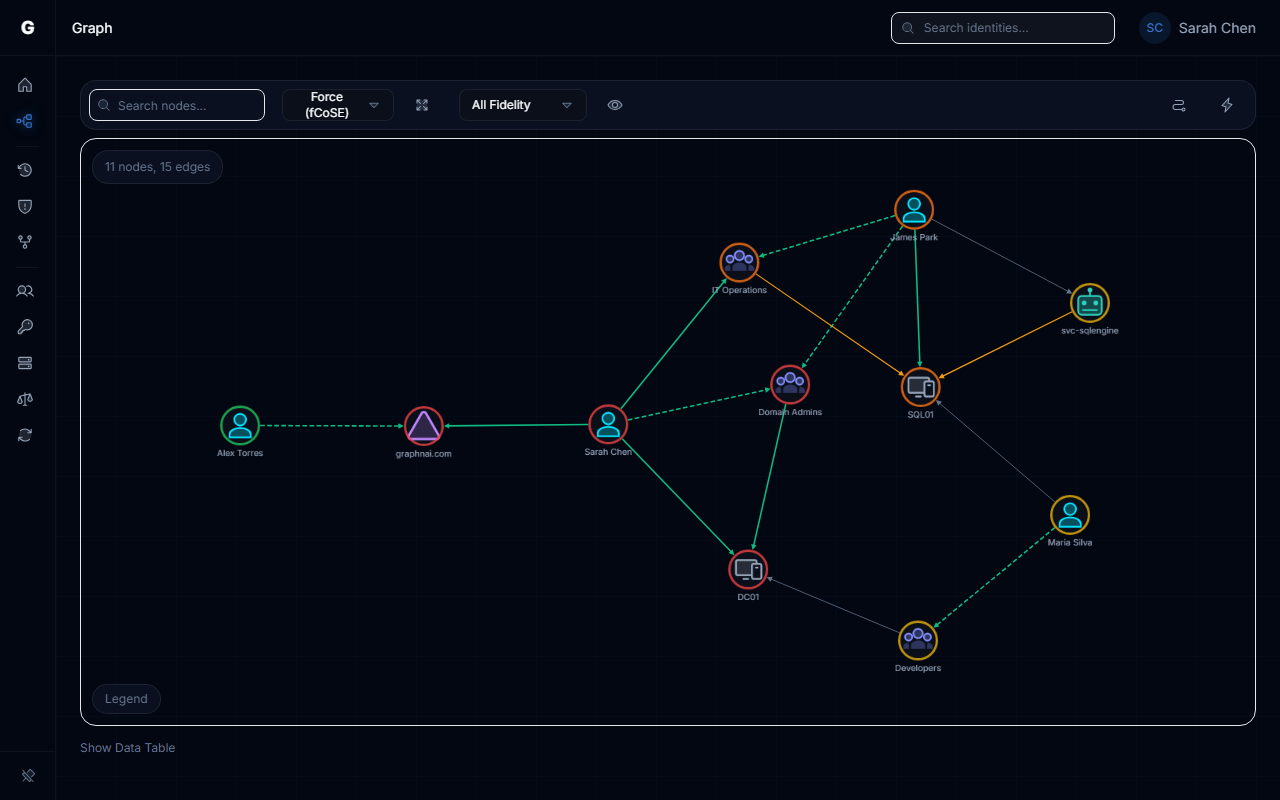
Every access relationship in the graph carries a fidelity tier. Three tiers. Simple.
Theoretical means the permission exists in configuration. A helpdesk technician is in a group with local admin rights on 200 workstations. That's a lateral movement surface, on paper. Configuration says the path exists, so we flag it.
Constrained means policy or network controls narrow it. Conditional access requires MFA from compliant devices. Network segmentation restricts which VLANs can reach those workstations. The permission is still there, but the blast radius is smaller than the raw ACL suggests.
Validated means telemetry proves the path is live. Authentication logs show the technician logged into 15 of those machines this week. That's not a theoretical finding anymore. That's an active lateral movement surface, and it goes to the top of the queue.
As telemetry flows in, relationships promote automatically. Your risk posture sharpens over time. No manual tuning. No threshold spreadsheets.
What This Actually Changes
- Your remediation queue drops to what's actually exploitable, not every theoretical path in AD
- Alert fatigue drops by 80%+ because unvalidated noise stops reaching your team
- You can show auditors exactly which access paths are confirmed live vs. speculative
- Your first sync delivers actionable findings within minutes. As telemetry flows in, fidelity sharpens automatically. No manual tuning required.
- Risk reports to the board show validated exposure, not theoretical paths that inflate numbers and erode trust.
See the full details in our Identity Graph docs.