Predictive Provisioning: Stop Toxic Combinations Before They Start
Simulate every access request against the identity graph before approval. Block dangerous combinations at the gate.
You spent weeks remediating over-permissions. The numbers looked great. Next quarter, they're back. Every approved access request quietly undoes the work. Predictive Provisioning breaks the cycle by simulating every request against the identity graph before it gets approved.
Over-Permission Analytics tells you who has too much access. You fix it. But provisioning keeps creating new over-permissions just as fast, because approvers don't have visibility into the graph. A new intern gets added to the Developers group. Perfectly reasonable, they're joining the team. What nobody saw is that the Developers group has GenericAll on a domain controller. That intern now has a direct path to Tier-0. A toxic combination was just created, and it sailed right through the approval workflow because the group membership looked fine in isolation.
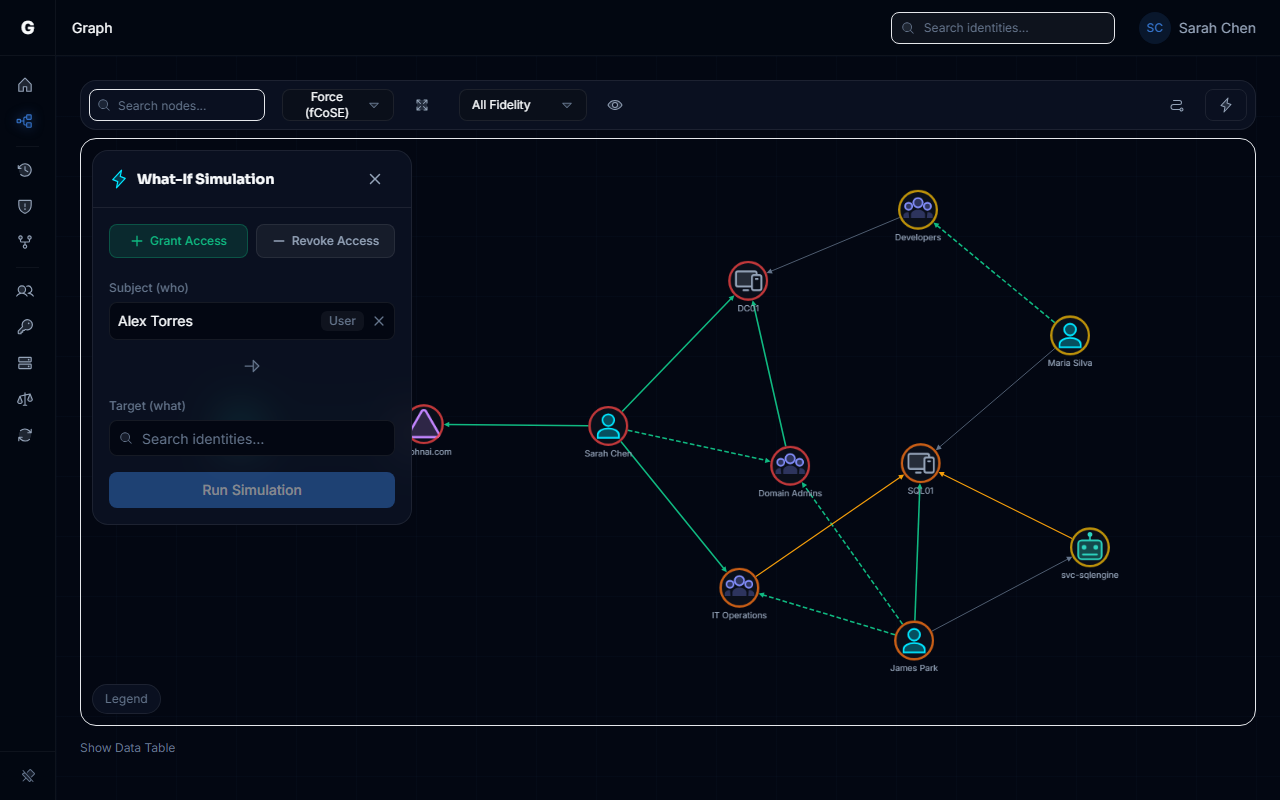
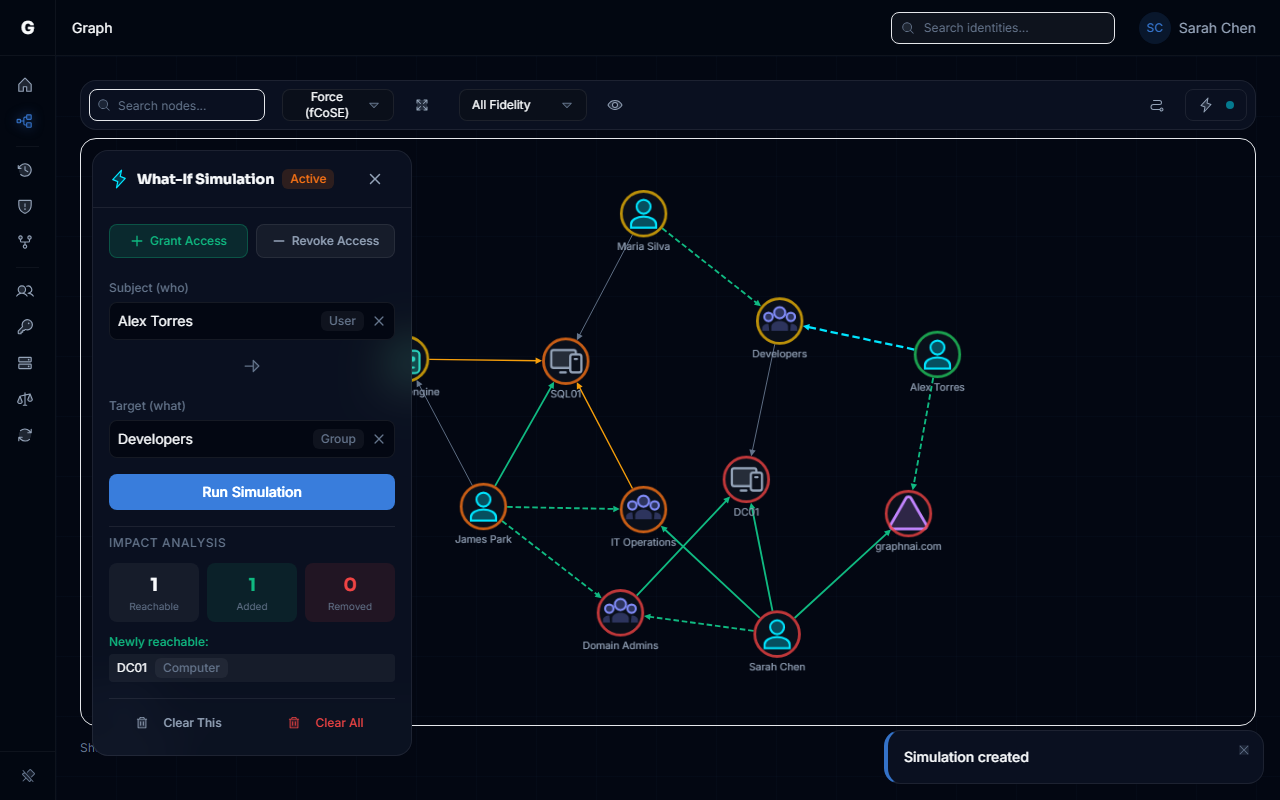
How It Works
Before the request gets approved, we simulate it against the identity graph. Automatically. The request goes into a delta overlay, and we answer the questions that weren't getting answered: Does this create a new path to Tier-0? Does it create a toxic combination? Does it violate separation of duty? Does it blow up the blast radius for this identity?
If the answer to any of those is yes, the approver sees exactly what would happen. Not a vague risk score. The actual graph paths, the affected assets, the specific combination that makes it dangerous.
It plugs into your existing IAM/IGA workflow via API. Your ticketing system doesn't change. Your approval process doesn't change. You just stop flying blind.
Why This Is Different
- Toxic combinations get caught at the gate, not six months later during an audit
- Approvers see the actual graph impact. Affected nodes, blast radius, Tier-0 paths. No more rubber-stamping in the dark.
- Over-permission findings stop growing because new access is validated before it's granted
- Drops into existing approval workflows. Your team keeps using the tools they already know.
- Prevention beats detection. Always has. This is how you get there for identity.
Documentation coming soon.