Identity Folding™: Collapse Complexity, Reveal What Matters
Consolidate millions of raw permission edges into clean, composite relationships you can actually read
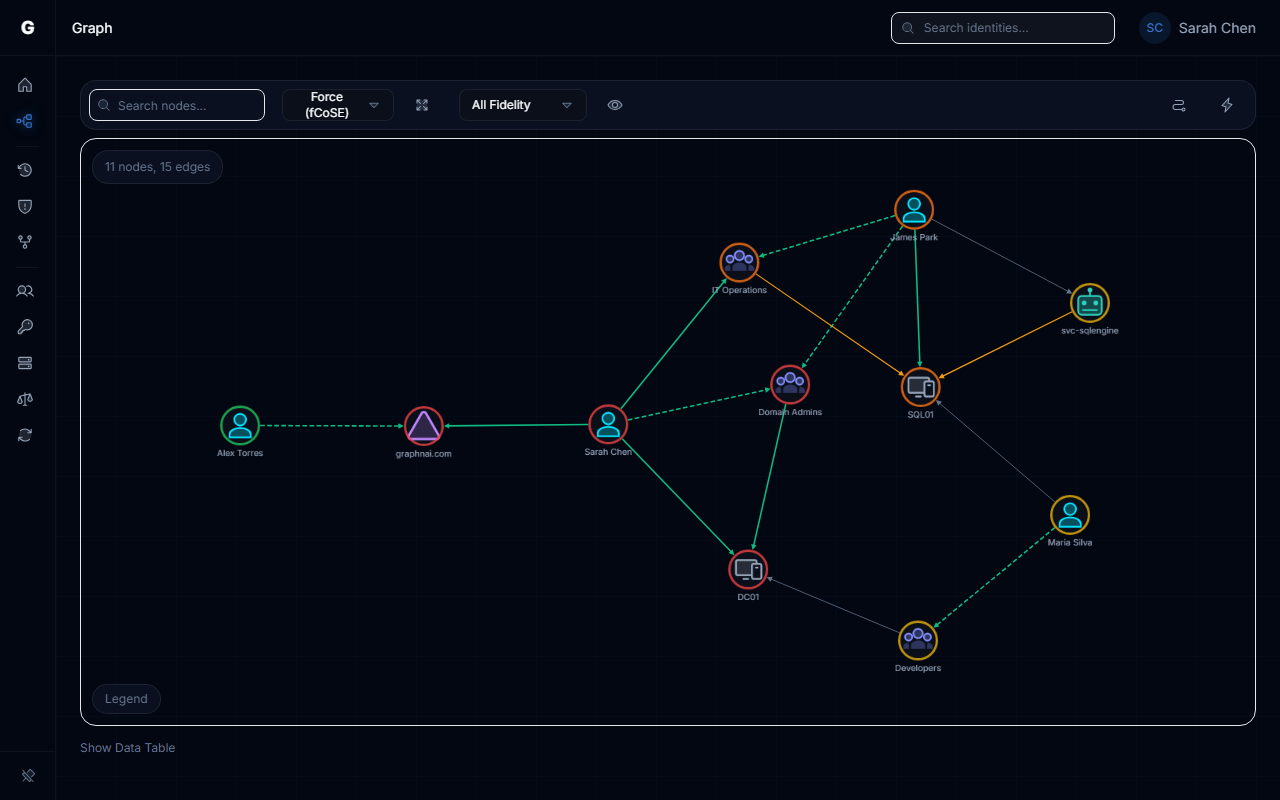
A typical identity environment generates millions of individual permission entries. Dozens of discrete permissions between the same two objects, repeated across thousands of identities. That's not visibility. That's noise.
We saw teams staring at graph visualizations that looked like a bowl of spaghetti. Most tools faithfully render every permission as its own edge. AD ACLs, Entra ID role assignments, OAuth2 grants. Technically correct. Practically useless. You can't find an attack path when you can't even see the graph.
How It Works
Identity Folding takes all permissions between the same two objects and consolidates them into a single composite edge. If a service account has GenericAll, WriteDACL, and WriteOwner on the same target, that's one edge, not three. The individual permissions are preserved inside a permissions array. Nothing is lost. The graph just becomes readable.
This works across permission sources. AD ACL entries, Entra ID abusable roles, OAuth2 grants, app role assignments. Each gets folded into the same composite model. The consolidation is severity-aware. Every permission type carries a severity tier based on real attack impact: Critical for full-control permissions like GenericAll and DCSync, down through High, Medium, and Low. The composite edge inherits the severity of its most dangerous permission.
The result is dramatic. Environments that produced millions of individual edges now render graphs a human can actually navigate. Query performance improves because the database is traversing composite edges instead of millions of individual ones. Attack path analysis becomes tractable.
Key Benefits
- Your graph goes from millions of edges to something a human can actually read. 10-100x reduction in visual noise.
- Every original permission is preserved in the permissions array. Drill in when you need the detail.
- Works across identity providers. AD ACLs, Entra ID roles, OAuth2 grants. Same consolidation model.
- Four severity tiers: Critical, High, Medium, Low. The composite edge shows the worst permission it contains.
- Query performance scales with composite edges, not raw permission count. Analysis that used to time out now completes in seconds.
Once edges are consolidated, Access Gravity scores each composite relationship by attack impact. See how it works in the Identity Folding guide.